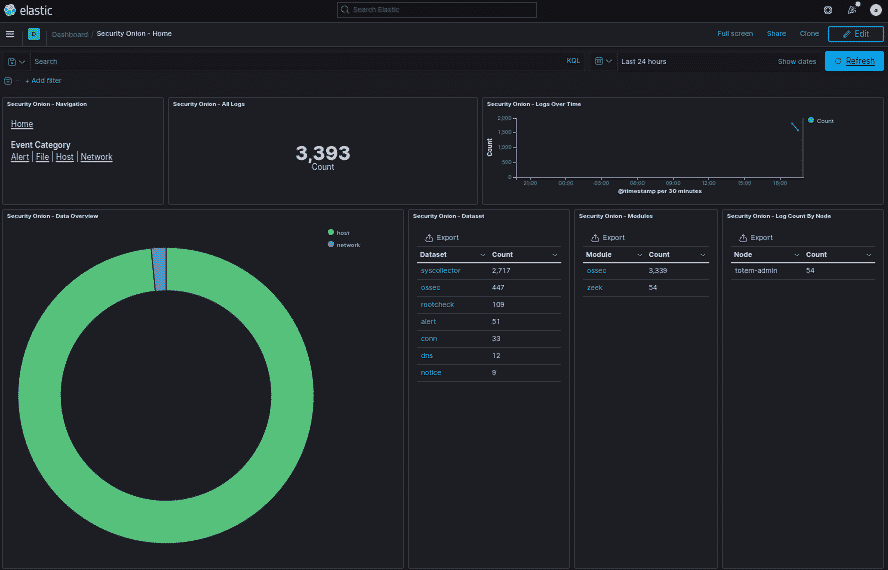
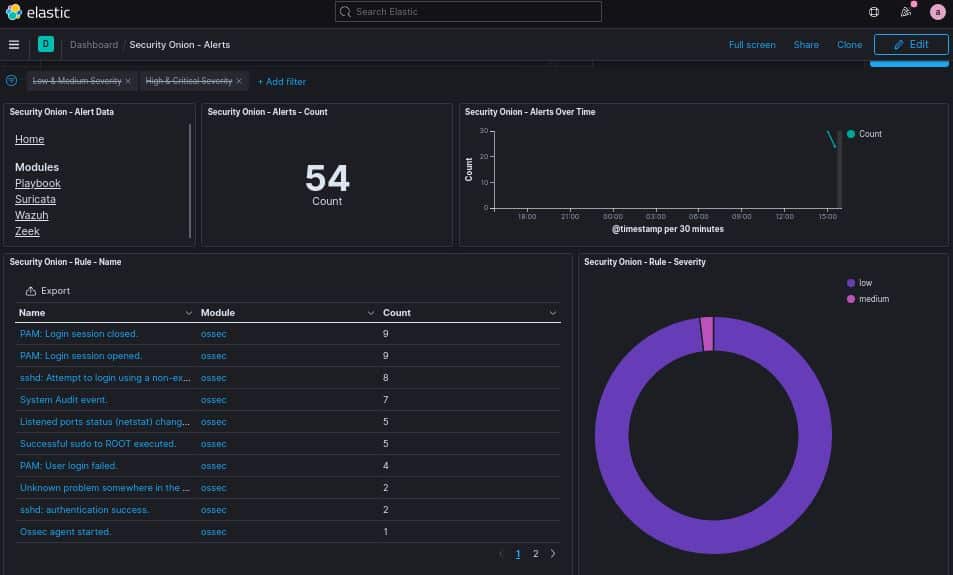
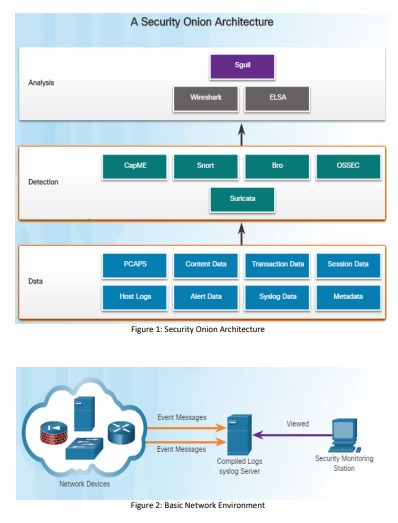
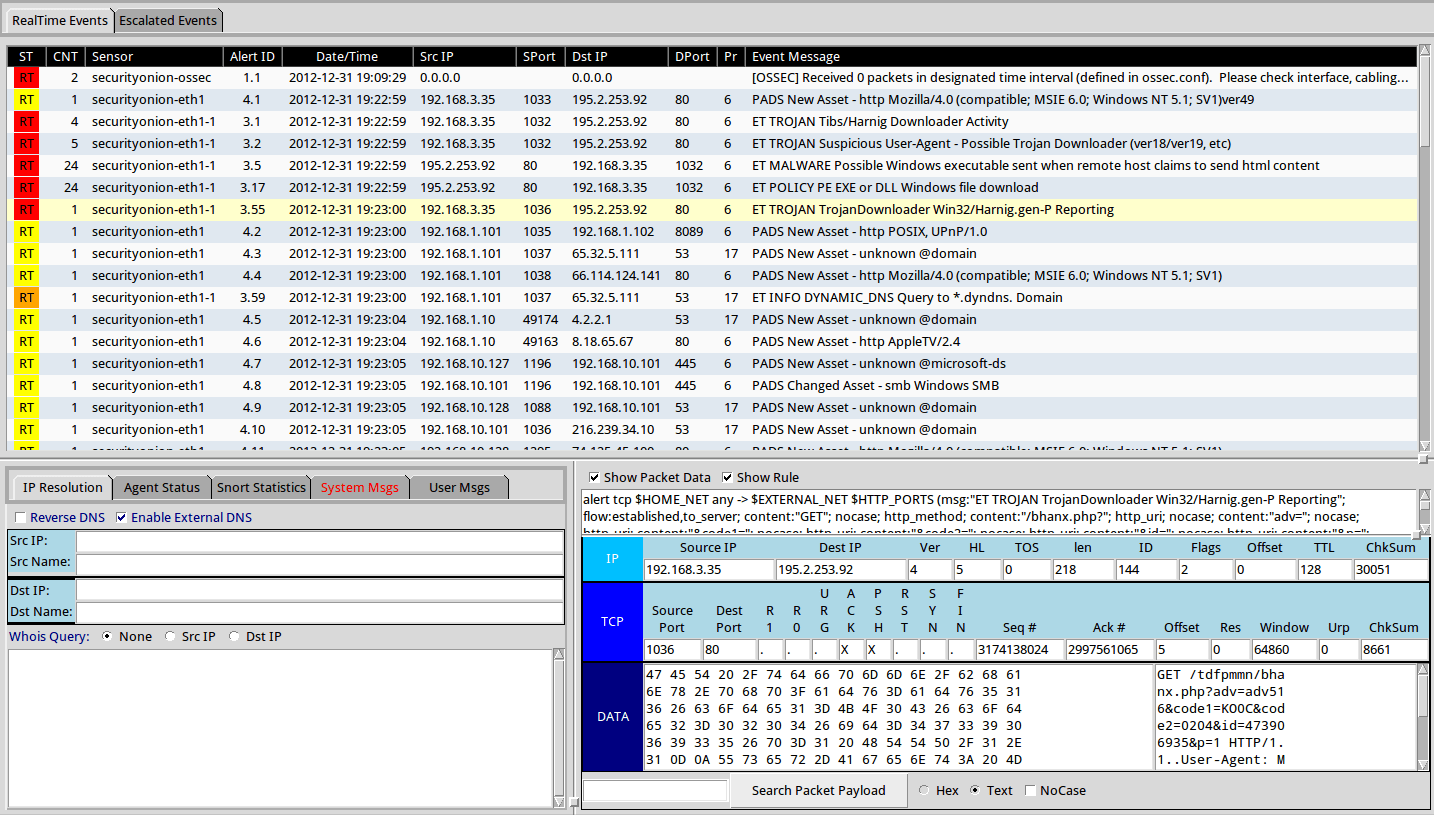
Experimental setup for Security Onion (SecOn) deployment for the SIEM... | Download Scientific Diagram

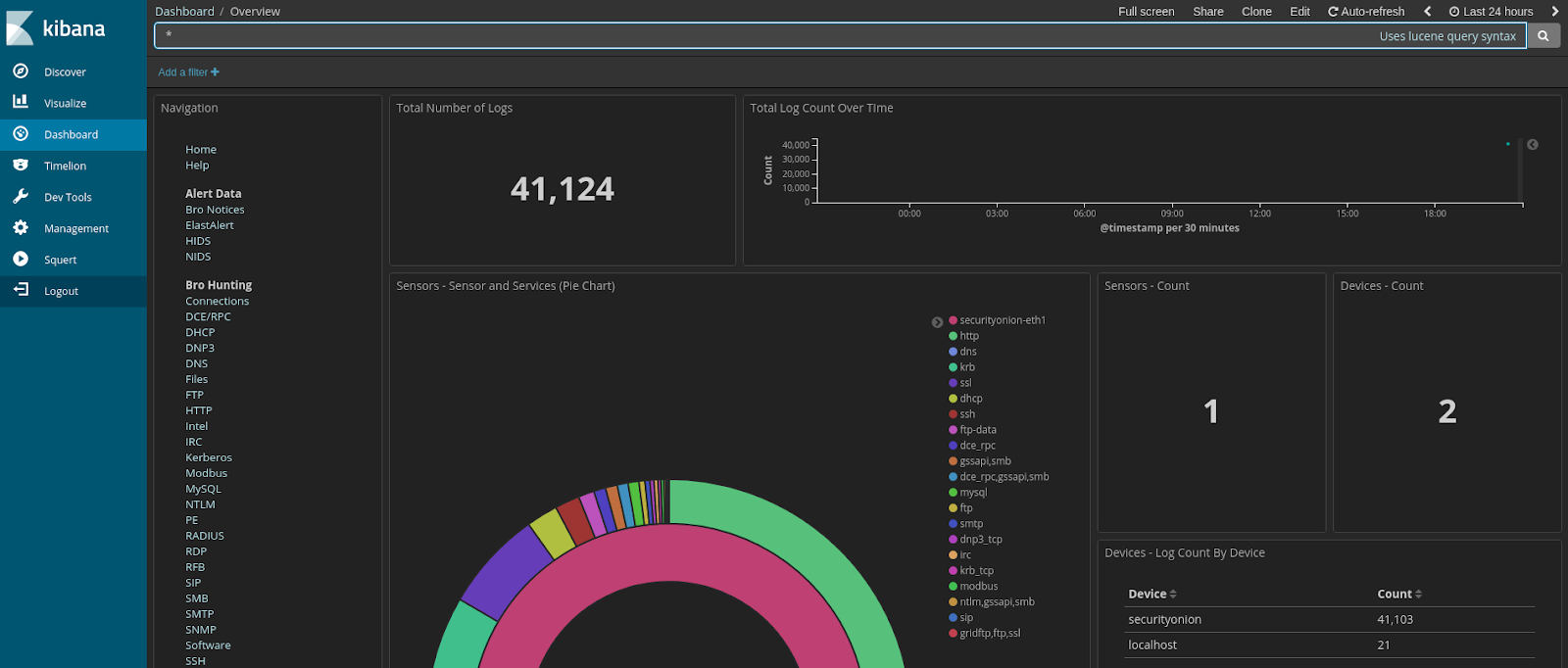
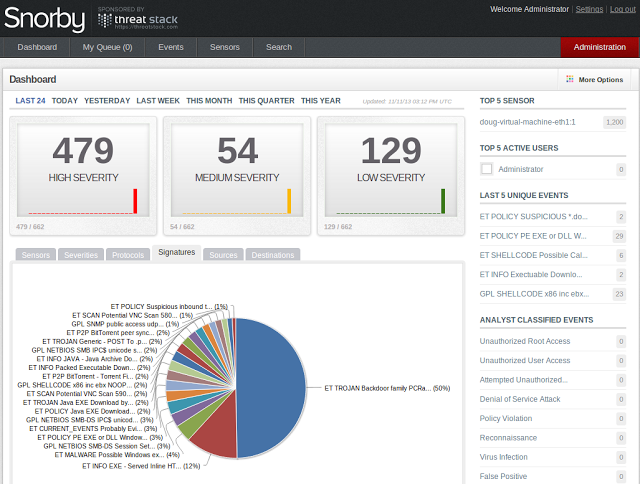
Simple Network Security Monitoring with Security Onion & NetWitness Investigator – CYBER ARMS – Computer Security

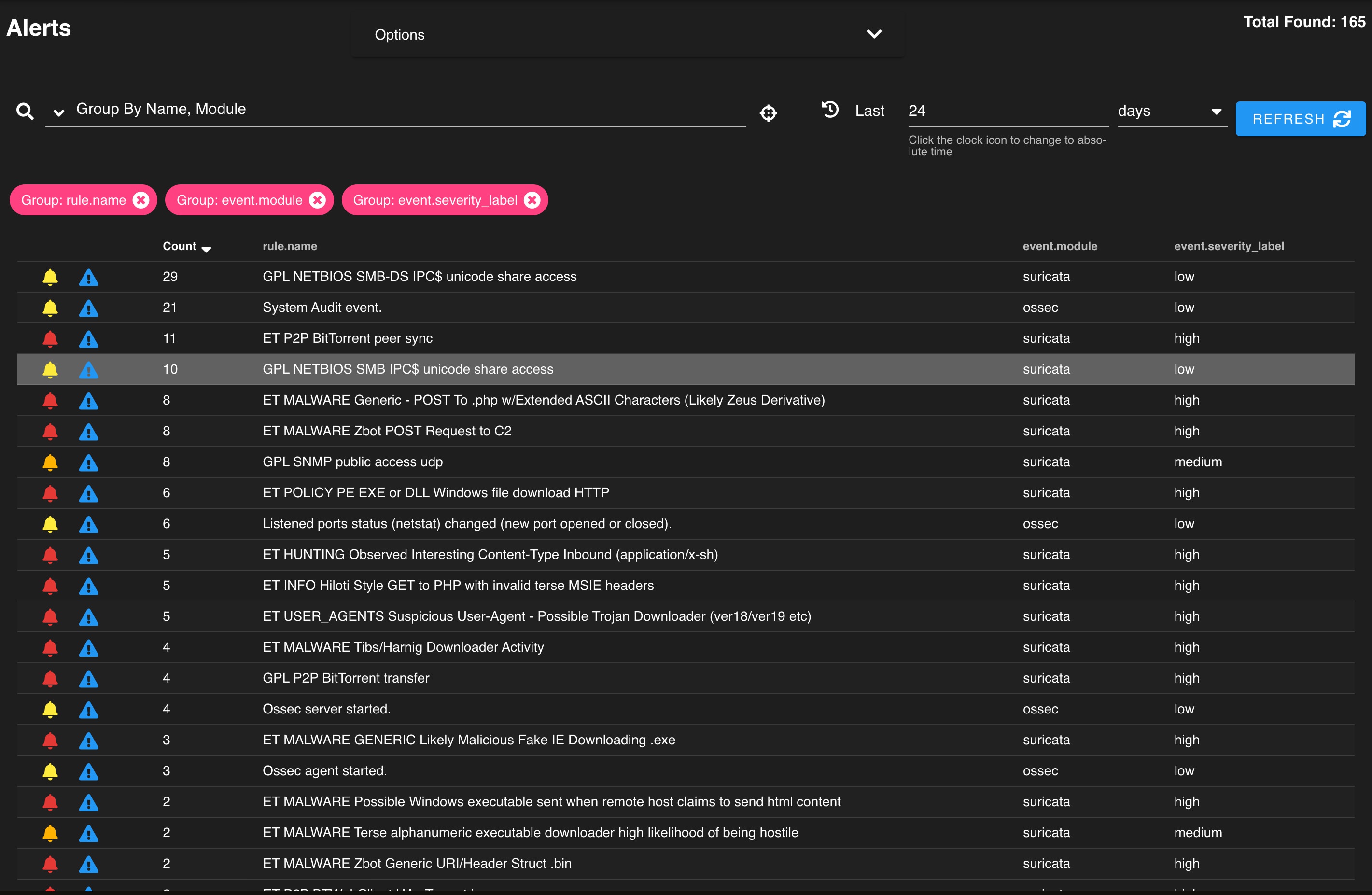
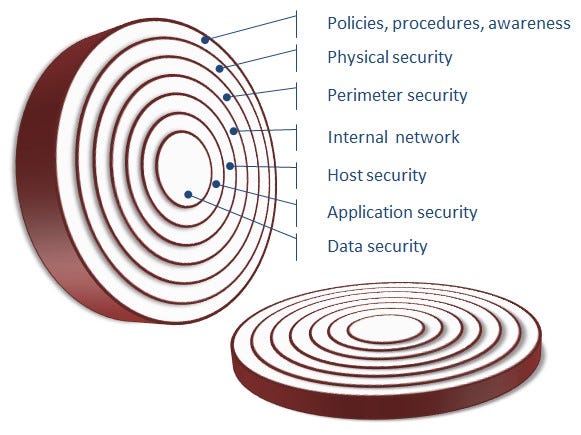
Sysmon & Security Onion, Part 2: Rise of Intelligence-Driven Computer Network Defense – Defensive Depth